Forewarned, forearmed; to be prepared is half the victory… Famous words from the greatest writer in the Spanish language, Miguel Cervantes. With everyone trying to jump on the digital bandwagon, hackers are having a field day. Recent studies have found that 54% of organizations have experienced an endpoint attack, and over 60% of attacks now use file-less hacking techniques. As enterprises transform their business landscape into digital platforms leveraging cloud computing, big data, mobile computing, and social media, traditional detection mechanisms need to transform too. Realtime Monitoring of information access and use, and its governance and oversight is the next step after designing an elaborate cybersecurity protection program.
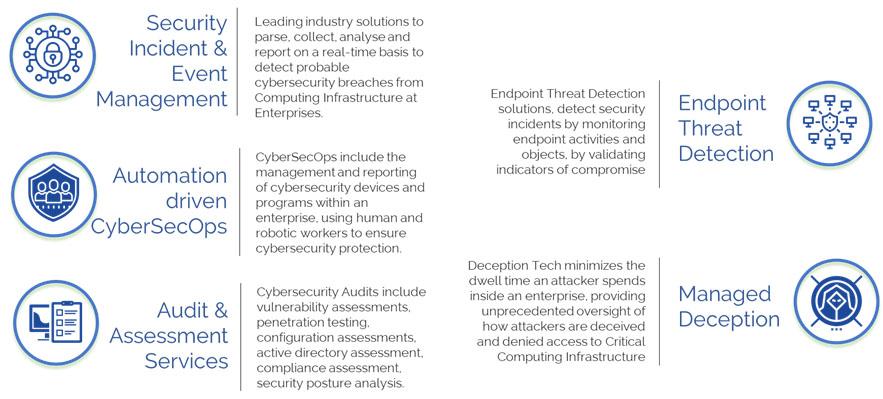
The CMS IT Services’ Detect portfolio is designed to support threat detection, compliance and security incident management through the collection and analysis (both near real-time and historical) of security events, as well as a wide variety of other event and contextual data sources. Our core capabilities are a broad scope of log event collection and management, the ability to analyse log events and other data across disparate sources, and operational capabilities (such as incident management, dashboards and reporting). All these are offered in 2 models.
CMS IT’s Integrated Cybersecurity Command Centre usually known as Integrated CyberSecurity Command Centre
Monitoring Remote Access during pandemic Response
Reduce Business Email Compromise by DNS Security
Automating reporting to know about non-compliance faster and without error
Stopping lateral movement in critical environment
Enhance granular control using Defensible Cyberspaces
Trend Micro Incorporated, a global leader in cybersecurity solutions, helps to make the world safe for exchanging digital information. Our Innovative solutions for consumers, businesses, and governments provide layered security for data centres, cloud environments, networks, and endpoints.
All our products work together to seamlessly share threat intelligence and provide a connected threat defense with centralized visibility and control, enabling better, faster protection.
With over 5,000 employees in over 50 countries and the world’s most advanced global threat intelligence, Trend Micro enables organizations to secure their journey to the cloud. For more information, visit www.trendmicro.com.
CMS IT work closely with Trend Micro in sales engagement and implementation process to take their technology to CMS IT customer base and beyond. We leverage our experience to understand how customers want to plug in best security solution to their information security requirement.
As a managed security service partner, CMS IT has a pool of experts to draw on their hands-on experience and insights in Trend Micro’s security portfolio.
Cisco is the worldwide leader in IT and networking. It helps companies of all sizes transform how people connect, communicate, and collaborate. Their product comprises of the following categories: Switches, Routers, Wireless, Network Management Interfaces and Modules, Optical Networking, Access Points, Outdoor and Industrial Access Points, Next-Generation Firewalls, Advanced Malware Protection, VPN Security Clients, Email, and Web Security.
We are a System Integrator and service provider of Cisco with PAN India presence. We have a large Cisco certified resource pool.
Ilantus has a unique product range in Identity management and Identity Governance and Administration. It is ahead of the curve in terms of technology. It is a SAAS product which is breaking all price barriers.
With CMS IT services having huge experience in EUC and cyber security, It is very easy to jump start your Identity and Access management with minimal effort and cost.
CyberArk is the global leader in privileged access security, a critical layer of IT security to protect data, infrastructure and assets across the enterprise, in the cloud and throughout the DevOps pipeline.
CyberArk delivers the industry’s most complete solution to reduce the risk created by privileged credentials and secrets. It is trusted by the world’s leading organizations, including more than 50 percent of the Fortune 500, to protect against external attackers and malicious insiders.
With CyberArk we secure enterprises against cyber-attacks that take cover behind insider privileges to attack critical enterprise assets. Together we deliver a new category of targeted security solutions that help leaders stop reacting to cyber threats and get ahead of them, preventing attack escalation before irreparable business harm is done.
Smokescreen brings military deception tactics to the digital battlefield. Their solutions protect some of the most highly targeted organisations globally, including leading financial institutions, critical infrastructure, and Fortune 500 companies.
They have the industry’s largest library of deception techniques. No one else covers pre-attack foot-printing, spear-phishing, web application attacks, social-engineering, data theft, Active Directory attacks, and more.
Our customers get far more than just the product — they get the Smokescreen play-book and our support. With tools and expertise, we guarantee we’ll reshape how you approach cybersecurity both strategically and tactically.
Fortinet provides top-rated network and content security, as well as secure access products that share intelligence and work together to form a cooperative fabric.
The unique Security Fabric combines Security Processors, an intuitive operating system, and applied threat intelligence to give you proven security, exceptional performance, and better visibility and control–while providing easier administration. The flagship product, enterprise firewall platform, FortiGate, is available in a wide range of sizes and form factors to fit any environment.
Complementary products that we resell along with FortiGate to enable a simplified, end-to-end security infrastructure cover:
Network Security – Protect the entire attack surface from headquarters to branch offices with advanced security.
Multi-Cloud Security – Complete visibility and control across the cloud that enables secure applications and connectivity.
Secure Access – Deliver secure application, device access, and management without compromising performance and speed.
Security Operations – Implement advanced threat intelligence to detect, prevent, and respond sophisticated malware and improve security awareness.
Network Operations – Leverage a smart security strategy that prioritizes automation-driven network operations that spots and prevents network breaches.
Endpoint and Device Protection – Proactive protection, visibility, and control for all endpoints and devices across the network.
Application Security – Protect critical business web applications with an integrated set of products to thwart advanced threats.
Ready to build a cyber resilient organization?
We’re here to help.












